Maximum of 25 job preferences reached.
Top Cybersecurity Jobs in Boston, MA
Machine Learning • Security • Software • Analytics • Defense
The Software Reverse Engineer will analyze vulnerabilities in cyber physical systems, reverse engineer software/firmware, develop cybersecurity solutions, and document research.
Top Skills:
Afl++Arm AssemblyBinary NinjaC/C++GhidraIda ProPythonQemuX86 Assembly
Machine Learning • Security • Software • Analytics • Defense
The Senior Cybersecurity Analyst supports operations, compliance, and security policies while providing expertise on cybersecurity strategy and governance.
Top Skills:
Anti-VirusAWSAzureCloud Access Security BrokerCorelight InvestigatorFirewallsIntrusion Detection SystemsIntrusion Prevention SystemsLinuxmacOSMalwareMicrosoft DefenderSentinelTcp/IpUnixVulnerability ManagementWindows
Machine Learning • Security • Software • Analytics • Defense
As a Senior Embedded Software Engineer, you will develop software applications, ensure quality through testing, integrate components, and communicate technical designs within a multidisciplinary team, focusing on embedded systems and cybersecurity.
Top Skills:
BashCC++DockerGccGitGitlabLlvmPythonQemuSubversionTcp/Ip
Machine Learning • Security • Software • Analytics • Defense
The Senior Reverse Engineer is responsible for analyzing and reversing complex software and firmware, developing automated tools, and collaborating on cyber solutions while ensuring national security.
Top Skills:
Afl++ArmAssembly LanguagesBinary NinjaC/C++GhidraIda ProPythonQemuX86
New
Cut your apply time in half.
Use ourAI Assistantto automatically fill your job applications.
Use For Free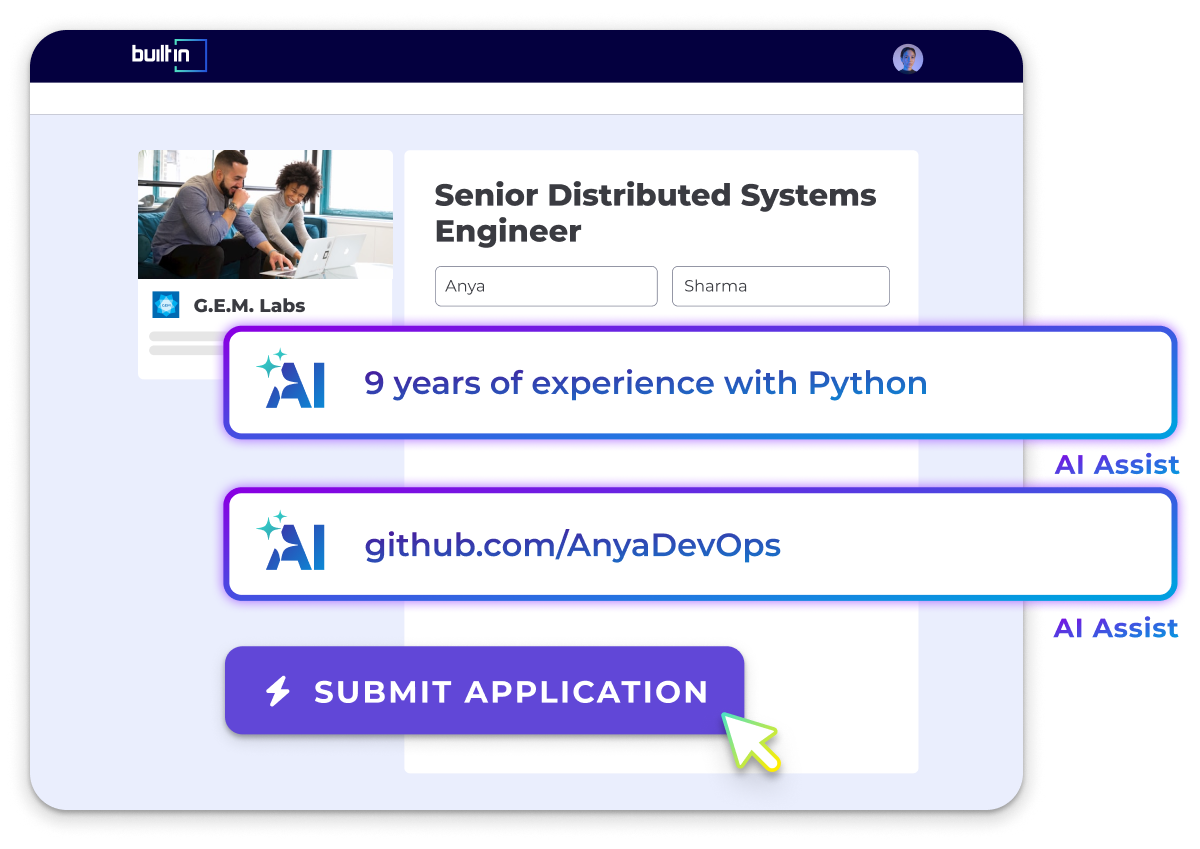

Let Your Resume Do The Work
Upload your resume to be matched with jobs you're a great fit for.
Success! We'll use this to further personalize your experience.
All Filters
Total selected ()
No Results
No Results


